In the continuously intertwining threads of our world and technology, the call for individuals versed in cybersecurity continues to amplify. Just as cyberspace constantly shifts and evolves, the field of cybersecurity adapts, presenting a myriad of roles and specializations. Allow us to lead you on a tour through the captivating universe of cybersecurity professions, shedding
Cybersecurity Industry: Tracking Market Trends and Growth
In the labyrinthine universe of technology, an industry is rapidly taking center stage. This formidable protagonist is none other than cybersecurity, a realm that safeguards our digital worlds from clandestine predators seeking to shatter our data sanctity. This piece aims to unfold the ever-expanding tableau of cybersecurity, meandering through the industry’s growth narrative, pioneering technologies
IoT Security News: Safeguarding Connected Devices
A kaleidoscopic assembly of devices – whether they be physical entities, automotive marvels, or towering buildings – finds itself woven into the intricate network we fondly term the “Internet of Things” (IoT). Layered with sensors and laced with advanced software, their communicative abilities overflow. They drink in vast quantities of data only to spew them
Phishing and Scam News: Identifying and Avoiding Cyber Threats
Immerse yourself in this chronicle, if you will, of the sinister dance between cyber predators and their unsuspecting prey. We’ll unravel a tapestry of online deceit, which unfurls its threads across the vast digital landscape. This narrative intricately weaves together tales of the latest machinations in phishing and scams, interspersed with strategies for resistance against
Data Privacy News: Navigating the Regulatory Landscape
In the tumultuous tides of our evolving digital landscape, data privacy stands as a bastion, a beacon of concern, central to both the common individual and the global corporate behemoth. It’s an ever-expanding, intricate tapestry woven from the threads of collected and processed personal information. The guardians of this tapestry, regulators, brandish their swords of
Cybersecurity Tech Updates: Strengthening Digital Defenses
As we hurl ourselves headlong into the undulating waves of technological advancement, the specter of cyberattacks looms, magnifying with our escalating reliance. A chameleonic enemy, cybercriminals continually metamorphose, devising innovative stratagems to infringe upon vulnerabilities, pilfering invaluable information. Enter the theatre of cybersecurity – a ceaseless battlefield where valiant protectors of digital realms vigilantly guard
Data Breach News: Uncovering the Latest Cyber Incidents in 2023
In the realm of the digital universe, an unseen menace lurks. It’s a ceaseless beast that claws at the gates of both businesses and individual privacy – data breaches. Recent months have painted a vivid tableau of these technological nightmares, served in a myriad of high-profile instances. Consider, for instance, the unfortunate saga of T-Mobile.
Malware and Virus Updates: Threats Lurking in Cyberspace
Immerse yourself in the intricate tapestry of our digital lives, stitched meticulously by the internet’s ceaseless loom. It has wrought a world revolutionized beyond recognition, yet it is not devoid of shadows. Among these shadows lurk malware and viruses, threats that beleaguer us with relentless frequency. Come, join me on a voyage through the labyrinth
Data Breach News: Uncovering the Latest Cyber Incidents
In our modern existence, the specter of data breaches is ubiquitous, insidious in its commonality. The ethereal dimension, the electronic world, the internet, is a battlefield. Confronted by shadowy figures of cybercrime, they continue to devise ingenious ways to illicitly obtain sensitive data from unsuspecting individuals and corporations. The ensuing narrative takes a deep dive
The Emergence of Quantum Computing and its Implications for Cybersecurity
Dive into the whirlpool of quantum computing, an innovation stirring up the status quo, hinged on the perplexing postulates of quantum mechanics. It is a double-edged sword, conceivably cracking labyrinthine conundrums currently too Gordian for our classical computers, yet it lurks, a shadowy specter posing newfound challenges to our cybersecurity landscape. Herein, we’ll delve deep
The Growing Threat of Cyber Warfare
In the intricate tapestry of our digitalized age, an ominous phantom, draped in binary, has risen — the specter of cyber warfare. A convoluted vortex, where, veiled under the cloak of state sponsorship or birthed within the machinations of nation-states, digital attacks transform into weapons of mass disruption. Their victims? Information systems, bedrocks of critical
The Rise of Privacy-Focused Technologies
In a world that trembles, teetering on the verge of virtual vulnerability, the invisible undercurrent of digital privacy threats, those looming specters of cyberattacks, the chilling onslaught of data breaches, and that peering, intrusive eye of surveillance practices, steadily proliferates. This eerie scenario, all too real and increasingly commonplace, echoes a resounding call, a veritable
The Evolution of Cybersecurity Regulations
In the current digital epoch, our ever-advancing terrain of technology necessitates robust bulwarks against cyber incursions. A multitude of cyber threats, both in terms of their burgeoning frequency and escalating sophistication, loom ominously, compelling both governments and industries to bring forth stringent regulations to shield valuable information, critical infrastructure, and unsuspecting consumers. This piece aims
The Rising Tide of Cyberattacks
In a world woven together by invisible threads of information, pulsating with the energy of interconnected data, the specter of cyberattacks is a chilling inevitability that looms large over the digital landscape. Each day, the rising tide of this malevolent force threatens individuals, corporations, and government bodies alike, its gnashing, monstrous waves growing increasingly sophisticated,
The Importance of Cybersecurity Training for Employees
We stand astride the precipice of the digital epoch, where entities—multifaceted, minuscule, or monstrous—find themselves beset by the omnipresent specter of cyber threats. Amidst the tumultuous landscape, a bastion, oft neglected but of paramount significance, springs forth: the education of employees about cybersecurity. Enter the intricate dance of teaching employees to safeguard the cyber realm.
The Role of Artificial Intelligence (AI) in Cybersecurity
As we traverse deeper into the digital universe, a nefarious menace is evolving in the shadows – cyberattacks. Their diversity, frequency, and intensity have skyrocketed, threatening to overtake traditional cybersecurity bastions. Desperate times call for novel solutions, and Artificial Intelligence (AI), cloaked in complexity and promise, emerges, promising an arsenal of enhanced cybersecurity strategies to
The Impact of the Internet of Things (IoT) on Cybersecurity
Picture this: everyday objects around you, whispering to each other in a language only they understand, exchanging data, and making decisions. That’s right, we’re talking about the Internet of Things (IoT), the unseen conductor of our symphony of progress. Oh, how it’s reshaped our existence, making us both spectators and participants in a dance where
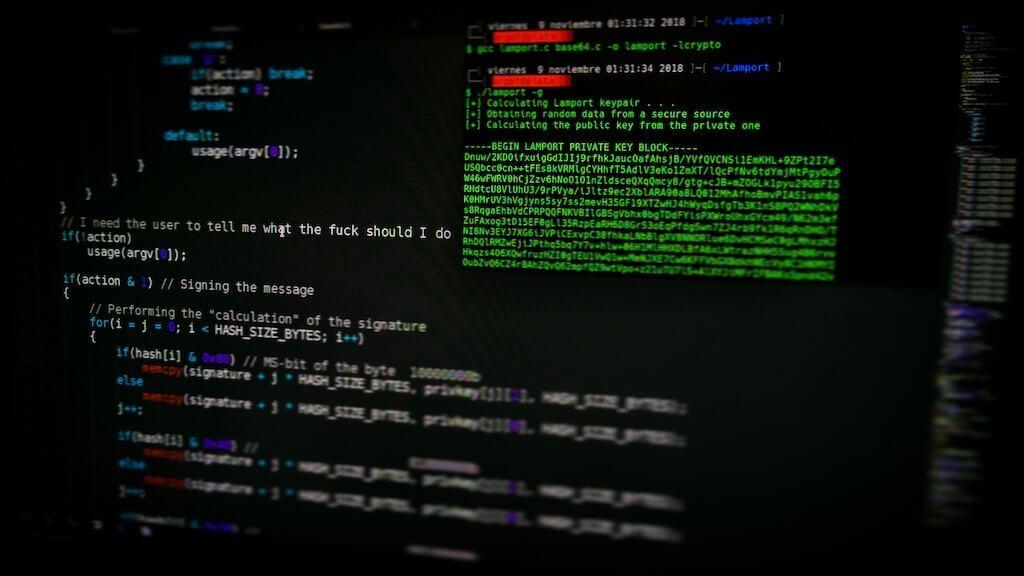
What Is Ransomware And How It Works?
Welcome, one and all, to our eclectic foray into the digital universe, a realm of ceaseless interconnectedness, a place where ones and zeroes dance a ceaseless waltz. But, with the advent of this modern epoch comes a deep, sinister underbelly: the increasing prevalence of cyber threats. Perhaps the most monstrous of these unseen terrors, dwelling
What Is A Phishing Attack?
Ponder, if you will, upon the shadowy world of digital deception where an innocuous looking email transforms into a pernicious phishing attack. Picture a missive, seemingly from an entity you trust, maybe a bank, or a cherished social media platform, or even a digital marketplace you frequent. Would you not be lured into a modicum
Microsoft Introduces GPT4 in Cybersecurity
On this remarkable day of April Fool’s, a groundbreaking revelation has been made by the tech giant, Microsoft. Brace yourself for the introduction of GPT4, an awe-inspiring generative AI model that is poised to assist and empower cybersecurity professionals in the intricate realm of safeguarding the most delicate sectors of industries, including hospitals, banks, offices,
The Ultimate Guide to Top Cyber Security Certifications in 2023
In the contemporary digital epoch, the realm of cybersecurity has ascended to paramount importance for organizations across the globe. As they endeavor to fortify their data and networks, enterprises are diligently seeking adept professionals equipped with the appropriate certifications. Within the confines of this textual composition, we shall embark upon an exploration of the preeminent
Best Wireless Security Cameras 2023
Ultimate Guide to the Top Wireless Security Cameras of 2023: A Comprehensive Review In the current year of 2023, the ever-expanding market has reached its saturation point with an overwhelming abundance of wireless security cameras. These innovative devices have been specifically engineered to safeguard and closely observe your residential abode. What sets these cameras apart
Top 50 Most Impersonated Brands in Phishing Attacks Worldwide
Phishing attacks exploit our trust in the brands we appreciate and use daily, making them increasingly difficult to detect, even for the most experienced digital users, according to Matthew Prince, co-founder and CEO of Cloudflare. Here is the complete ranking of the 50 most impersonated brands (based on data from 2022): AT&T Inc. PayPal Microsoft
How Can I Secure My Internet Connection?
Unraveling the Mysteries: Empowering Cyber Shielding for Your Online Connection In this rapidly evolving digital epoch, the quintessential necessity of fortifying your internet connection has acquired unprecedented significance. With the extensive reservoir of personal information perpetually stored and exchanged within the online realm, the disconcerting reality looms large—hackers and cybercriminals surreptitiously penetrate the veil of
How to protect your privacy online
In the digital epoch that constantly undergoes transformation, the matter of online privacy has ascended to a paramount position, demanding our unwavering attention. The protection of personal information in the vast expanse of the internet has become equally indispensable for individuals as well as companies, who strive to ensure the fortification of their users’ data.
The 10 most common types of cyberattacks
Unleashed into the digital realm, a swirling vortex of cyber attacks has erupted in recent years, engulfing the global landscape with an ominous presence. These attacks, like insidious shadows, cast doubt upon the authenticity of threats, blurring the line between reality and hyperbole. The surge of cyberattacks has propelled them to the forefront of modern